How To Setup Ldap Server On Windows
First published on MSDN on Apr 10, 2017
Step-by-step guide for setting up LDAPS (LDAP over SSL)
The guide is split into 3 sections :
- Create a Windows Server VM in Azure
- Setup LDAP using AD LDS (Active Directory Lightweight Directory Services)
- Setup LDAPS (LDAP over SSL)
NOTE : The following steps are like for Windows Server 2008, 2012, 2012 R2 , 2016. In this article, we will use Windows Server 2012 R2.
Create a Windows Server VM in Azure
Create a VM named "ldapstest" Windows Server 2012 R2 Datacenter Standard DS12 using the instructions hither: Create a Windows virtual machine with the Azure portal
Connect to the VM ldapstest using Remote Desktop Connectedness.
Setup LDAP using AD LDS
Now allow us add Advert LDS in our VM ldapstest
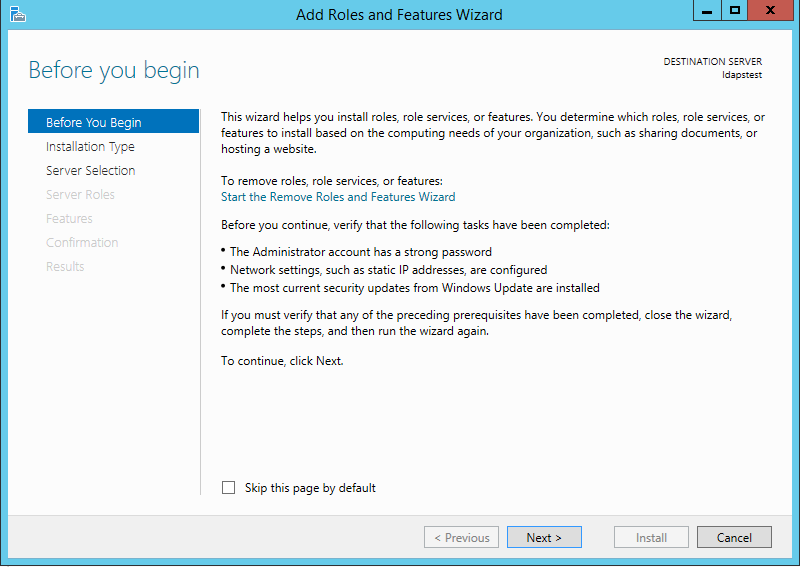
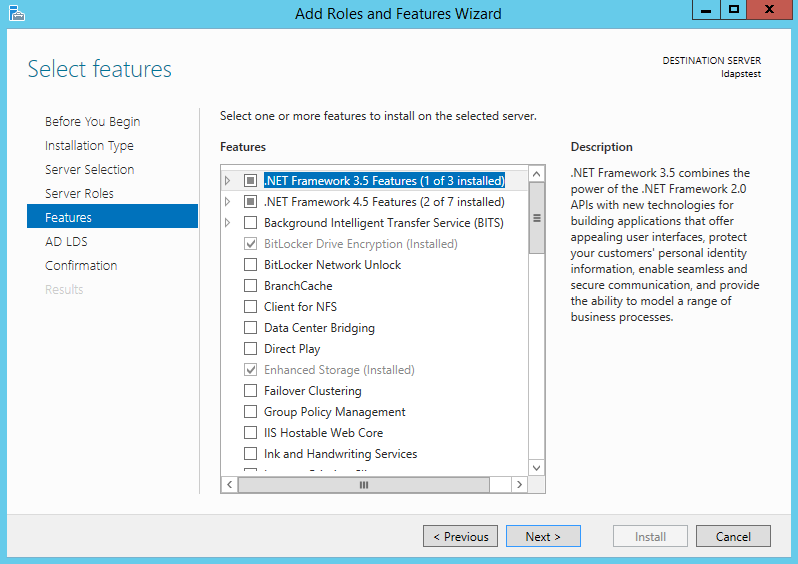
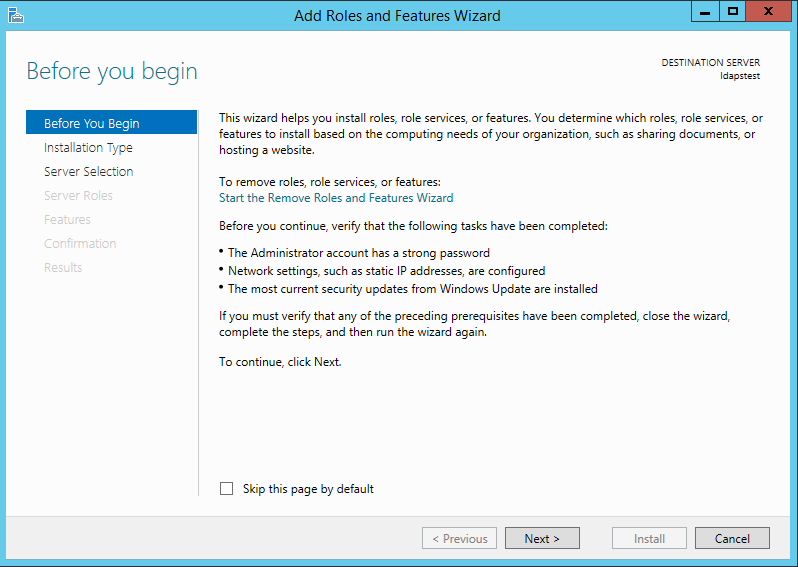
Click on Kickoff --> Server Manager --> Add Roles and Features. Click Side by side.
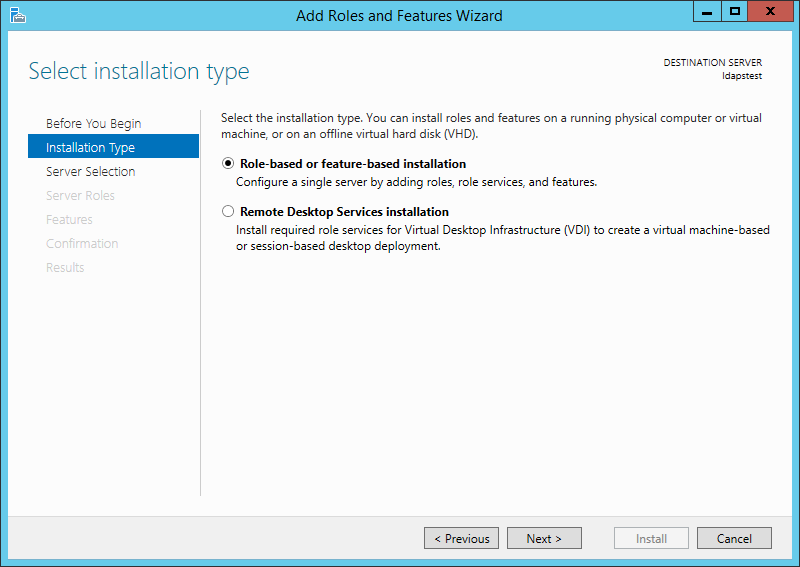
Cull Role-based or feature-based installation. Click Adjacent.
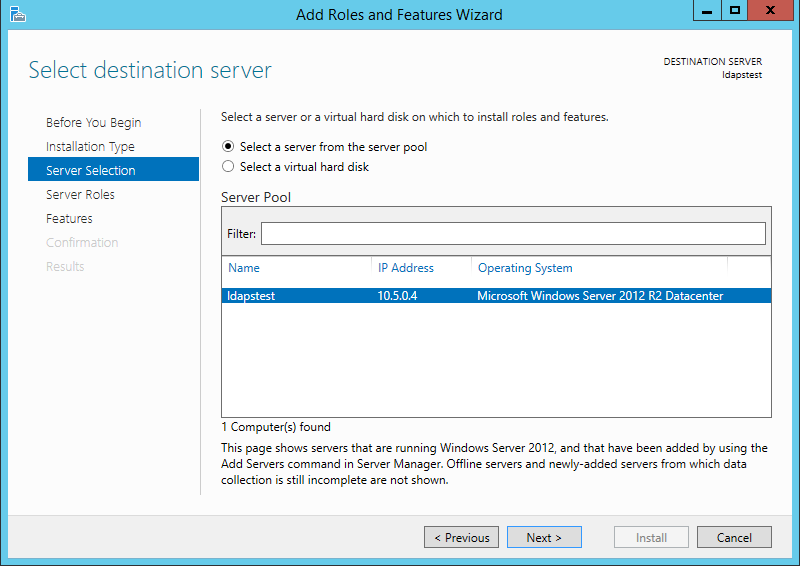
Select ldapstest server from the server puddle. Click Side by side.
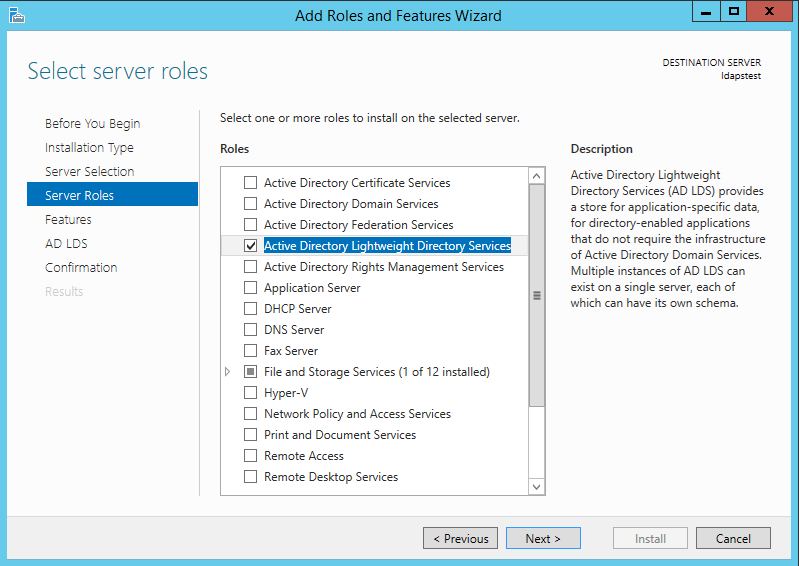
Mark Agile Directory Lightweight Directory Services from the listing of roles and click Next.
From the list of features, choose null – but click Next.
Click Side by side.

Click Install to start installation.

Once installation is consummate, click Close.

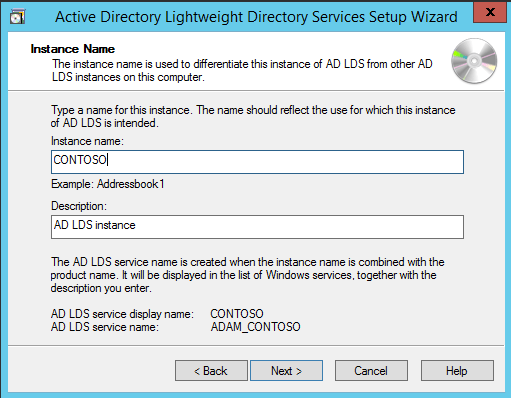
Now we have successfully fix Advertizing LDS Function. Let us create a new Advertisement LDS Instance "CONTOSO" using the wizard. Click the "Run the Active Directory Lightweight Directory Services Setup Magician" in the above screen. And then Click Close.

Choose Unique Instance since nosotros are setting it upwardly for the first fourth dimension.

Blazon "CONTOSO" in Case Name and click Next.
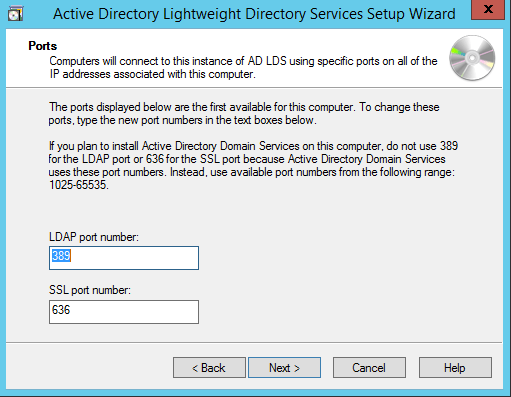
By Default, LDAP Port is 389 and LDAPS port is 636, let us choose the default values - click Adjacent.
Create a new Awarding Directory Partition named "CN=MRS,DC=CONTOSO,DC=COM". Click Adjacent.

Using the default values for storage location of ADLDS files- Click Next.

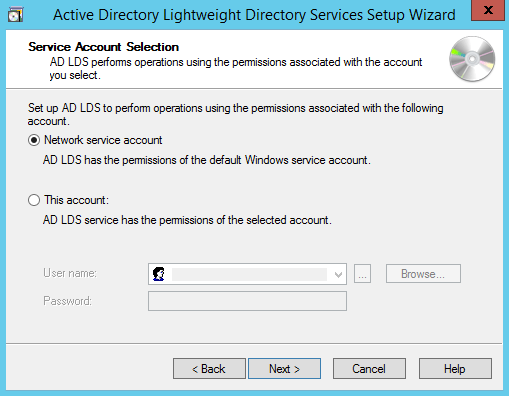
Choosing Network Service Account for running the AD LDS Service.
You will receive a prompt warning about information replication. Since we are using a single LDAP Server, we can click Yes.

Choosing the currently logged on user every bit an ambassador for the AD LDS Instance. Click Next.

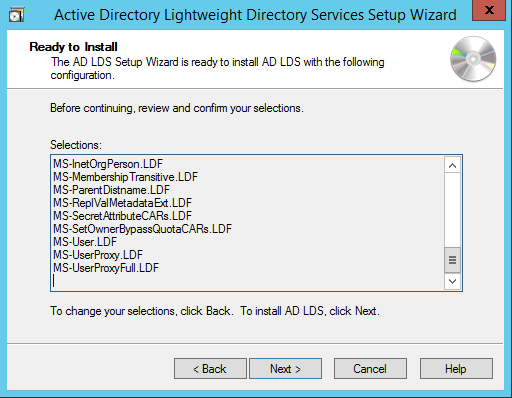
Mark all the required LDIF files to import (Here we are marking all files). Click Next.

Verify that all the selections are right and so Click Next to confirm Installation.
Once the case is setup successfully, click Terminate.

Now permit united states endeavour to connect to the AD LDS Instance CONTOSO using ADSI Edit.
Click on Start --> Search "ADSI Edit" and open it.
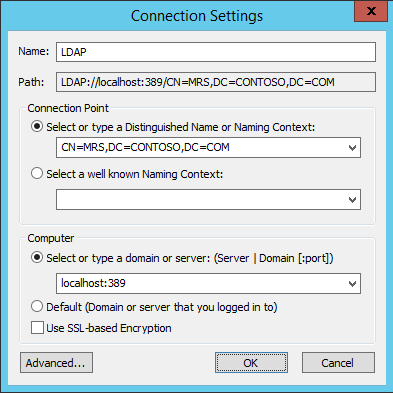
Right Click on ADSI Edit Binder (on the left pane) and choose Connect To.. . Fill the following values and Click OK.
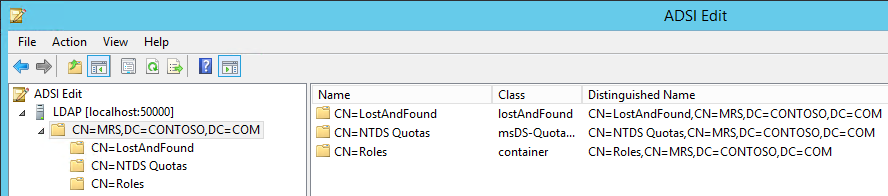
If the connexion is successful, we will be able to browse the Directory CN=MRS,DC=CONTOSO,DC=COM :
Setup LDAPS (LDAP over SSL)
The Certificate to be used for LDAPS must satisfy the following iii requirements:
• Certificate must be valid for the purpose of Server Authentication. This ways that it must as well contains the Server Hallmark object identifier (OID): 1.3.6.ane.5.five.seven.3.1
• The Discipline name or the first proper noun in the Bailiwick Alternative Proper name (SAN) must match the Fully Qualified Domain Name (FQDN) of the host machine, such as Subject:CN=contosoldaps. For more information, see How to add together a Subject Alternative Proper noun to a secure LDAP certificate .
• The host machine business relationship must take access to the private central.
At present, permit's utilize Agile Directory Certificate Services to create a certificate to exist used for LDAPS. If yous already have a certificate satisfying the above requirements, you lot can skip this step.
Click on Kickoff --> Server Manager --> Add Roles and Features. Click Next.
Choose Part-based or feature-based installation. Click Next.

Select ldapstest server from the server pool. Click Next.

Choose Agile Directory Certificate Services from the list of roles and click Next.

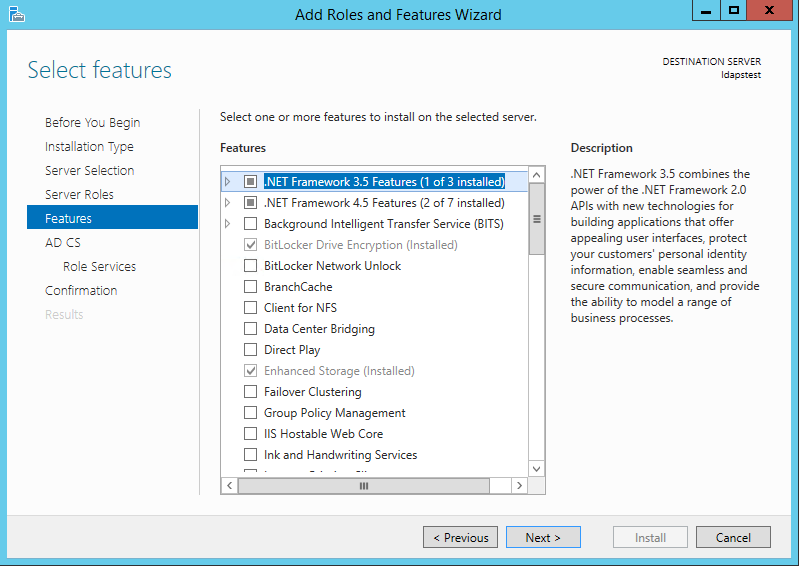
Choose nothing from the list of features and click Next.
Click Adjacent.

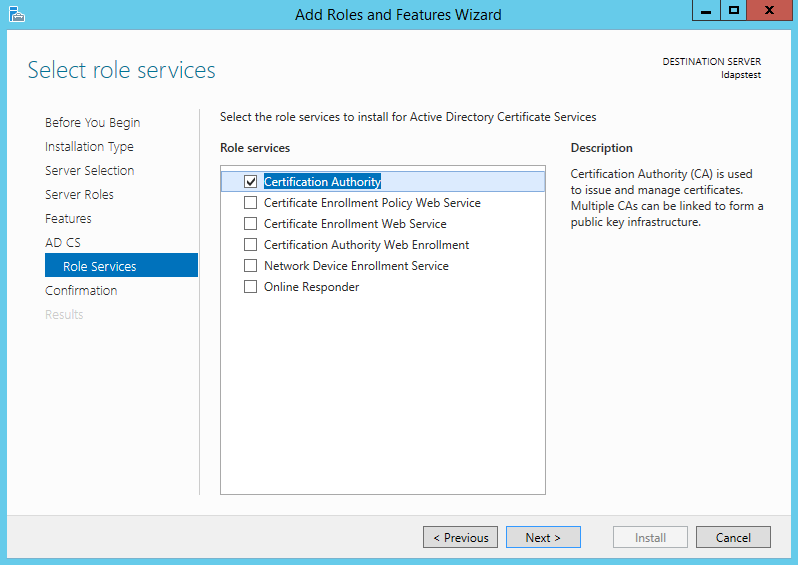
Marking "Certificate Authority" from the listing of roles and click Next.
Click Install to ostend installation.

In one case installation is complete, Click Close.

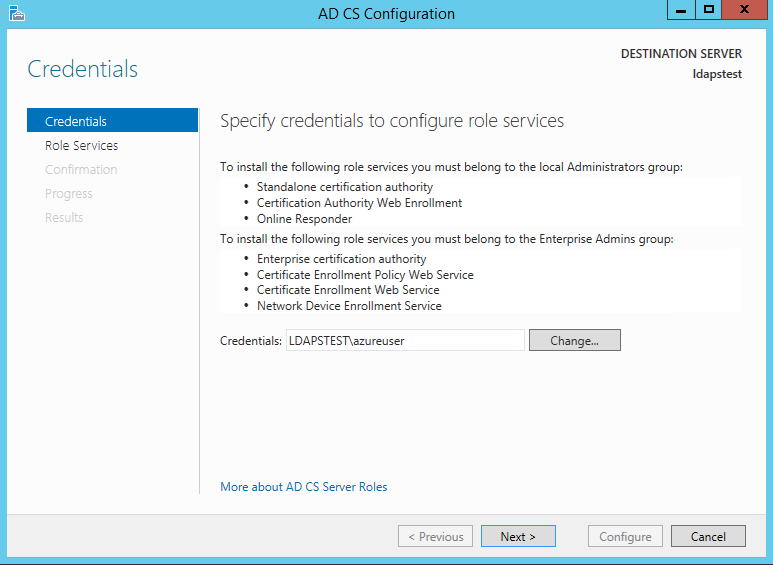
Now let's create a certificate using AD CS Configuration Wizard. To open the wizard, click on "Configure Active Directory Document Services on the destination server" in the to a higher place screen. And then click Shut. Nosotros can apply the currently logged on user azureuser to configure office services since it belongs to the local Administrators group. Click Next.
Choose Certification Say-so from the list of roles. Click Next.

Since this is a local box setup without a domain, we are going to choose a Standalone CA. Click Next.

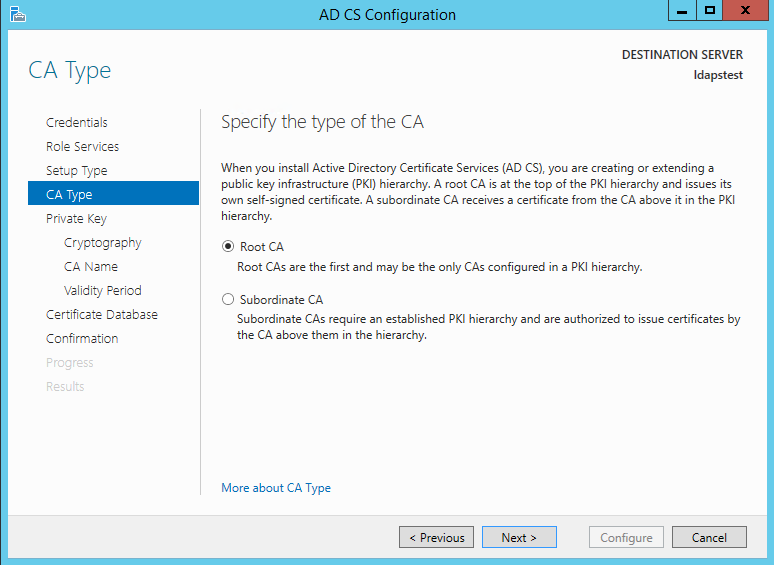
Choosing Root CA equally the type of CA, click Next.
Since we do not possess a individual fundamental – permit's create a new 1. Click Next.

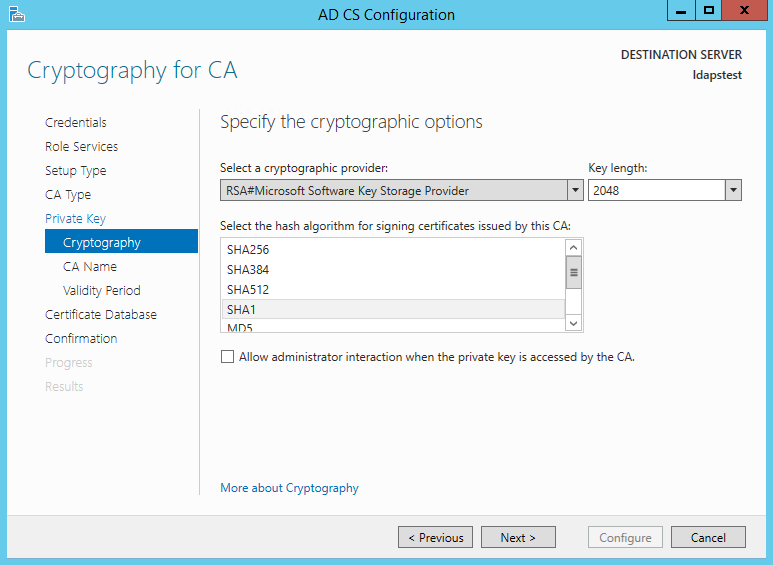
Choosing SHA1 as the Hash algorithm. Click Next.
UPDATE : Recommended to select the almost recent hashing algorithm since SHA-one deprecation countdown
The name of the CA must friction match the Hostname (requirement number 2). Enter "LDAPSTEST" and Click Next.

Specifying validity period of the certificate. Choosing Default 5 years. Click Side by side.

Choosing default database locations, click Next.

Click Configure to ostend.
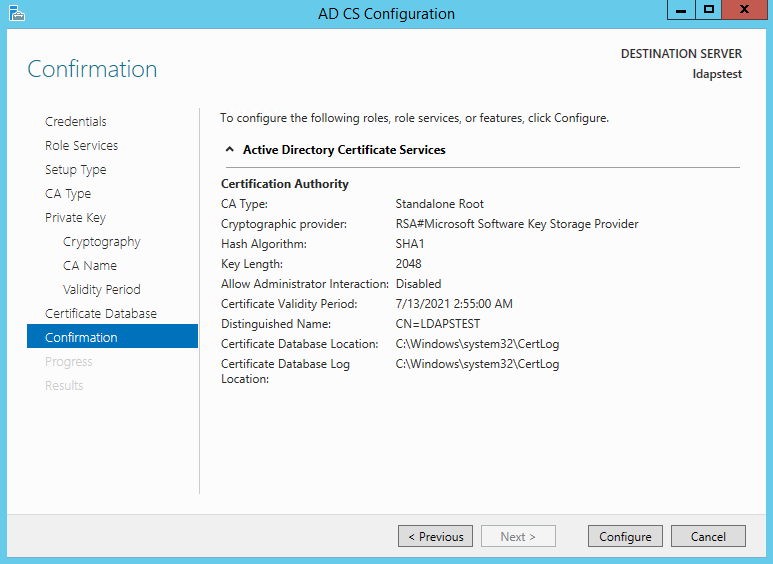
In one case the configuration is successful/complete. Click Close.

Now let usa view the generated document.
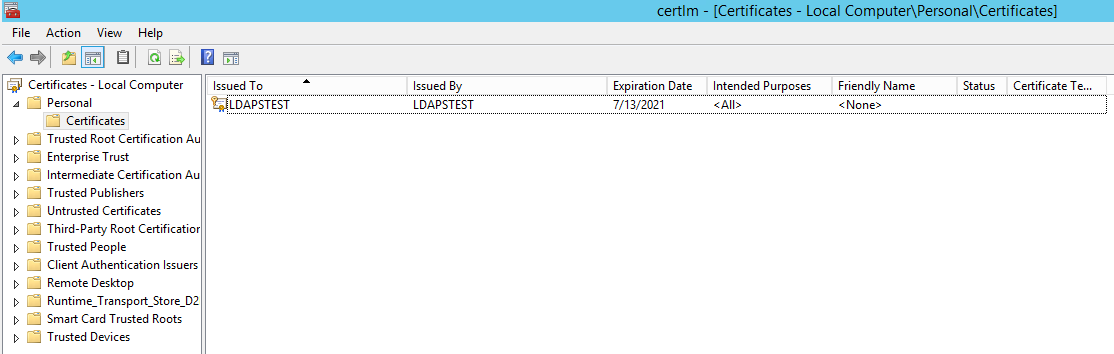
Click on Starting time à Search "Manage Computer Certificates" and open it.
Click on Personal Certificates and verify that the document "LDAPSTEST" is present:
Now to fulfill the third requirement, permit united states of america ensure host automobile account has access to the private key. Using the Certutil utility, find the Unique Container Proper name. Open Command Prompt in Ambassador mode and run the post-obit command: certutil -verifystore MY

The private key will be present in the following location C:\ProgramData\Microsoft\Crypto\Keys\<UniqueContainerName>
Right Click C:\ProgramData\Microsoft\Crypto\Keys\874cb49a696726e9f435c1888b69f317_d3e61130-4cd8-4288-a344-7784647ff8c4 and click backdrop --> Security and add read permissions for NETWORK SERVICE.

Nosotros need to import this certificate into JRE fundamental store since our certificate "CN=LDAPSTEST" is not signed by whatsoever past any trusted Certification Authority(CA) which is configured in yous JRE keystore e.g Verisign, Thwate, goDaddy or entrust etc. In society to import this certificate using the keytool utility, let united states get-go export this cert equally a .CER from the motorcar certificate store:
Click Showtime --> Search "Manage Estimator Certificates" and open up it. Open up personal, right click LDAPSTEST cert and click "Consign".

This opens the Certificate Export Sorcerer. Click Next.

Do non consign the private cardinal. Click Next.

Cull Base of operations-64 encoded X .509 file format. Click Adjacent.

Exporting the .CER to Desktop. Click Next.

Click Terminate to complete the document consign.

Certificate is at present successfully exported to "C:\Users\azureuser\Desktop\ldapstest.cer".
Now we shall import it to JRE Keystore using the keytool command present in this location:
C:\Programme Files\Coffee\jre1.8.0_92\bin\keytool.exe.
Open up Command Prompt in ambassador mode. Navigate to "C:\Program Files\Java\jre1.viii.0_92\bin\" and run the post-obit control:
keytool -importcert -alias "ldapstest" -keystore "C:\Program Files\Coffee\jre1.8.0_92\lib\security\cacerts" -storepass changeit -file "C:\Users\azureuser\Desktop\ldapstest.cer"

Type "yes" in the Trust this certificate prompt.
In one case document is successfully added to the JRE keystore, we can connect to the LDAP server over SSL.
At present let us try to connect to LDAP Server (with and without SSL) using the ldp.exe tool.
Connection strings for
LDAP:\\ldapstest:389
LDAPS:\\ldapstest:636
Click on Start --> Search ldp.exe --> Connection and fill in the post-obit parameters and click OK to connect:
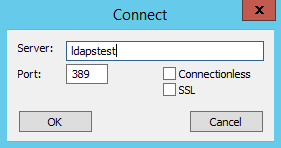
If Connexion is successful, you volition see the following message in the ldp.exe tool:

To Connect to LDAPS (LDAP over SSL), utilise port 636 and marking SSL. Click OK to connect.

If connection is successful, you will encounter the following message in the ldp.exe tool:

REFERENCES
https://technet.microsoft.com/en-us/library/cc770639(v=ws.10)
https://technet.microsoft.com/en-the states/library/cc725767(5=ws.10).aspx
http://social.technet.microsoft.com/wiki/contents/articles/2980.ldap-over-ssl-ldaps-document....
https://blogs.technet.microsoft.com/askds/2008/03/13/troubleshooting-ldap-over-ssl/
http://javarevisited.blogspot.com/2011/11/ldap-authentication-agile-directory.html
Source: https://techcommunity.microsoft.com/t5/sql-server-blog/step-by-step-guide-to-setup-ldaps-on-windows-server/ba-p/385362
Posted by: mcknightbeficest1967.blogspot.com

0 Response to "How To Setup Ldap Server On Windows"
Post a Comment